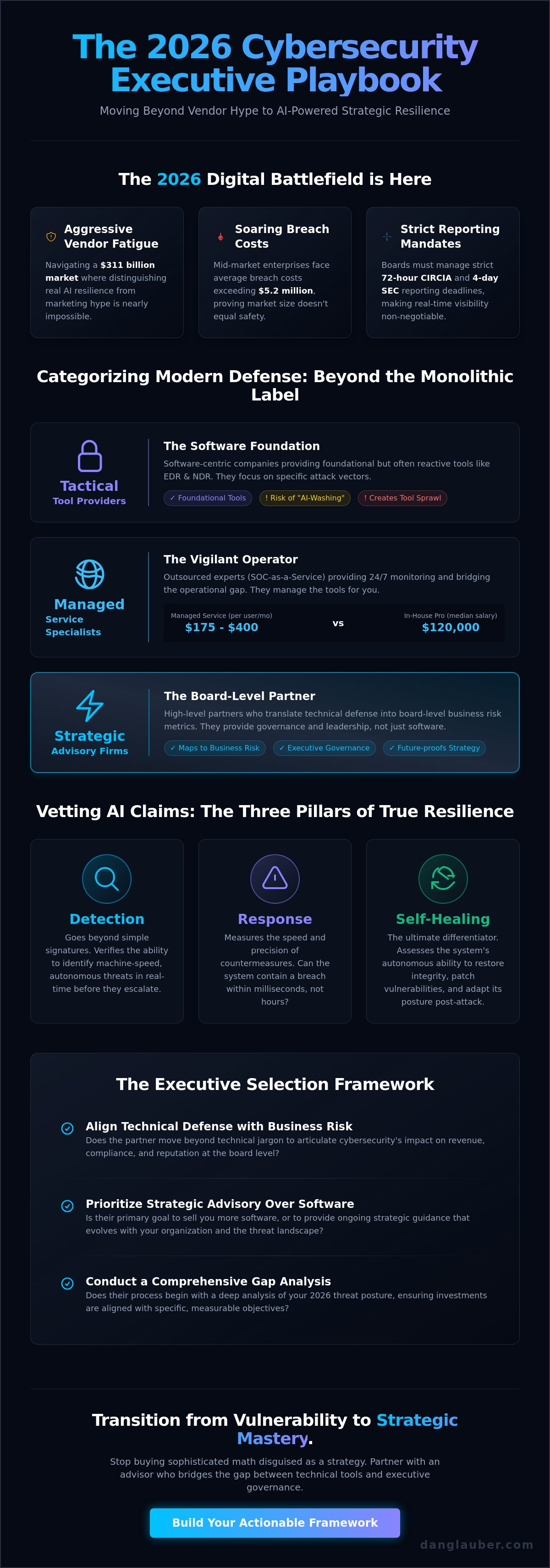
Most cybersecurity companies in 2026 are selling you sophisticated math disguised as a strategy, leaving your board vulnerable to the very risks they claim to mitigate. You've likely experienced the exhaustion of vendor fatigue, where aggressive sales tactics make it nearly impossible to distinguish between actual AI resilience and empty marketing hype. It's a common frustration for leaders who must manage the strict 72-hour reporting mandates of CIRCIA and the FCC's identity verification rules while facing breach costs projected to exceed $5.2 million for mid-market enterprises.
I will help you move from a state of vulnerability to one of strategic mastery by providing an actionable framework for executive selection. You'll gain a clear categorization of the $311 billion market and a rigorous checklist for vetting "agentic AI" claims. This guide ensures you identify partners that offer strategic advisory rather than just software, allowing you to bridge the gap between technical toolsets and board-level business risks at the intersection of AI and cybersecurity.
Key Takeaways
- Categorize the vendor landscape into strategic advisors and tactical tool providers to move beyond superficial industry rankings.
- Verify AI-driven defense claims by auditing for the three pillars of resilience: detection, response, and autonomous self-healing capabilities.
- Apply a structured selection framework to vet cybersecurity companies based on their ability to map technical defense to board-level business risks.
- Transition from a "set-and-forget" software mindset to a leadership-driven model that prioritizes strategic advisory and governance.
- Conduct a comprehensive gap analysis of your 2026 threat posture to ensure security investments align with specific organizational objectives.
Beyond the List: Navigating the 2026 Cybersecurity Company Ecosystem
Static lists of the "Top 100" cybersecurity companies are relics of a pre-autonomous era. In 2026, the staggering volume of data breaches, which now cost mid-market firms over $5.2 million, proves that market size doesn't equate to organizational safety. You aren't just looking for a vendor; you're selecting a strategic partner capable of countering machine-speed attacks. This selection requires a fundamental shift. You must move from viewing security as a technical line item to treating it as a core pillar of executive governance and resilience.
A comprehensive overview of cybersecurity principles reveals that defense must evolve as quickly as the threats it faces. Modern cybersecurity companies must now provide more than just signature-based detection. They must offer a bridge between technical depth and strategic leadership. As the global market scales toward $311 billion this year, the primary differentiator isn't the number of features. It's the ability to translate complex neural network activity into actionable board-level risk metrics that drive business decisions.
The 2026 Digital Battlefield
The proliferation of Adversarial AI has fundamentally altered the digital battlefield. Legacy models that rely on manual human intervention are obsolete when faced with autonomous agents that pivot through networks in milliseconds. Today, Zero-Trust Architecture is the baseline requirement for any viable partner. Every vendor you vet must demonstrate a "never trust, always verify" posture that extends deep into their own software supply chain. With the SEC requiring material incident disclosure within four business days, board-level visibility is a non-negotiable feature. You need partners who provide a real-time, high-fidelity view of your risk posture, ensuring you're prepared for the scrutiny of the "Age of Artificial Intelligence."
Why Traditional Tool Sprawl is the New Vulnerability
Managing 50 or more disconnected security vendors creates a fragmented defense that sophisticated attackers easily exploit. The hidden cost isn't just the licensing fees; it's the cognitive load on your staff and the dangerous latency in your response times. Integration-first companies are winning because they prioritize data harmony over niche functionality. Tool sprawl in 2026 represents a critical operational risk where the sheer volume of disconnected security layers creates blind spots that autonomous agents exploit faster than human teams can correlate data. Success in this environment requires consolidating your stack into a unified, actionable framework that prioritizes visibility and speed over mere tool accumulation.
Categorizing Modern Defense: Strategic vs. Tactical Cybersecurity Firms
Selecting the right partners in 2026 requires you to look past the monolithic labels used by most industry rankings. The market has fractured into three distinct tiers: tactical tool providers, managed service specialists, and strategic advisory firms. Understanding where your organization sits on the maturity curve is the first step toward effective governance. Many leaders find themselves over-invested in tools but under-invested in the leadership required to orchestrate them. Benchmarking your current posture against the NIST Cybersecurity Framework provides the baseline necessary to identify whether you need more "boots on the ground" or a better "command and control" structure.
The tactical tier consists of software-centric cybersecurity companies focused on specific attack vectors. These include Endpoint Detection and Response (EDR) and Network Detection and Response (NDR) specialists. While these tools are foundational, they're often reactive. Managed services, such as SOC-as-a-Service, bridge the gap by providing 24/7 monitoring. With advanced security packages for managed services now ranging from $175 to $400 per user per month, the cost of outsourced vigilance is significant but often lower than the $120,000 median salary required for a single in-house professional. However, even the best SOC cannot replace the high-level risk management provided by strategic partners.
Tactical Vendors: The Software Foundation
When you evaluate tactical software, scalability is paramount. You must prioritize cloud-native, API-first architectures that allow for seamless data exchange across your entire tech stack. The most dangerous trap in 2026 is "AI-washing," where legacy vendors rebrand basic automation as advanced neural networks. Real AI defense must demonstrate autonomous detection and self-healing capabilities. If a vendor cannot provide technical proof of how their models handle adversarial AI attacks, they're likely selling marketing hype rather than true resilience. Mastering these domains requires more than a software license; it demands an actionable framework tailored to your specific organizational needs.
Strategic Partners: The Governance Layer
Mid-to-large organizations are increasingly shifting toward virtual CISO consulting services to provide the leadership software lacks. A strategic advisor doesn't just manage alerts; they translate technical telemetry into business value for the board. These firms typically operate on retainers ranging from $2,500 to $15,000 per month, offering a level of expertise that bridges the gap between IT and the C-suite. By focusing on the "Intersection of AI and Cybersecurity," these partners ensure that your defense strategy evolves alongside emerging threats. They provide the governance necessary to turn a collection of disconnected tools into a unified, resilient shield against modern attack vectors.
Evaluating AI Resilience: The Core Differentiator in 2026
In the current digital battlefield, the term "AI-powered" has become a hollow marketing claim used by nearly all cybersecurity companies to signal modern relevance. True AI resilience, however, isn't about having a chatbot in the dashboard. It's about a system's ability to maintain its integrity while under direct attack from autonomous agents. As you move through the selection process, you must demand technical proof of how a vendor's neural networks perform when their training data is poisoned or their logic is manipulated. Following the NIST guidance on choosing a cybersecurity provider ensures you're vetting these claims against a rigorous, government-backed standard rather than relying on a sales deck.
Mastering the intersection of AI and cybersecurity requires a focus on three distinct pillars of resilience: detection, response, and self-healing. Detection must be predictive, identifying zero-day attack patterns before they execute. Response must be instantaneous, leveraging agentic AI to isolate compromised segments in milliseconds. Finally, self-healing capabilities allow systems to automatically roll back unauthorized changes and patch vulnerabilities in real time. Beyond these technical pillars, you must audit a firm's data privacy standards. Ensure that your proprietary data isn't being used to train a vendor's Large Language Models (LLMs) without explicit, granular consent and robust anonymization protocols.
Adversarial AI and Neural Network Defense
The most sophisticated defense platforms now prioritize adversarial AI testing as the gold standard for security efficacy. These systems are designed to detect and neutralize AI-generated deepfakes and hyper-personalized social engineering campaigns that bypass traditional filters. Machine learning models must be trained to recognize the subtle "digital fingerprints" of synthetic content that human eyes cannot perceive. Adversarial AI in 2026 is a critical threat vector where malicious actors manipulate neural network inputs to bypass security protocols or force incorrect model outputs. Without specific countermeasures against these tactics, your AI defense is merely a faster version of a legacy firewall.
The Human-in-the-Loop Requirement
Fully autonomous security systems offer unprecedented speed, but they lack the strategic context necessary for high-stakes decision making. The most effective cybersecurity firms maintain a "human-in-the-loop" architecture to balance rapid response with clinical accuracy. You should evaluate the ratio of automated actions to human expert interventions within a vendor's platform. A system that is too automated risks catastrophic false positives that disrupt business operations, while a system that is too manual will fail against machine-speed threats. Look for partners who use AI to augment human intelligence, allowing your team to focus on strategic risk management rather than chasing endless low-level alerts.
The Executive Selection Framework: How to Vet a Cybersecurity Partner
Vetting cybersecurity companies requires a repeatable methodology that moves beyond the surface-level claims found on community forums or marketing brochures. You must approach selection as a military commander evaluates a strategic ally. It's about trust, interoperability, and shared objectives. A flawed partnership doesn't just waste budget; it creates a false sense of security that leaves your critical infrastructure exposed to autonomous attack vectors. This framework provides the discipline necessary to separate high-performance partners from those selling legacy solutions in modern packaging.
Your first step is aligning security goals with organizational business objectives. Security shouldn't exist in a vacuum. It must enable business continuity and regulatory compliance. Next, conduct a rigorous gap analysis of your current 2026 threat posture, specifically looking at how you handle the February 2026 CISA directive on end-of-life edge devices. Once you've identified the gaps, vet the vendor's "AI Integrity." Demand transparency on how they manage data handling for LLMs and whether they can prove their models haven't been compromised by adversarial training. Finally, assess the long-term viability of the firm. You must demand a roadmap that accounts for the September 11, 2026, EU Cyber Resilience Act reporting deadline and the final CMMC rule established in November 2025.
The Board-Level Vetting Checklist
Executive leadership needs more than technical telemetry; they require actionable frameworks that translate risk into financial and operational impact. When vetting a partner, ask if they provide clear risk reporting that a non-technical board can understand. You should also verify how the vendor quantifies ROI. Is it through reduced insurance premiums or prevented downtime? A critical 2026 challenge is the "Shadow AI" crisis, where employees use unauthorized generative tools. Your partner must have a definitive strategy for identifying and securing these hidden neural networks within your organization. To ensure your current defenses are up to standard, you can request a strategic risk assessment today.
Local vs. Global: The vCISO Advantage
In a remote-first world, the value of localized strategic leadership remains immense. Organizations often find success by prioritizing vCISO services in Orlando or other regional hubs to ensure compliance with specific state and local regulations. While global toolsets provide the "firepower" of advanced EDR and NDR, a local strategic advisor provides the "boots on the ground" leadership necessary to navigate complex regional compliance landscapes. This balance allows you to leverage world-class software while maintaining a partner who understands the unique geopolitical and economic risks affecting your specific headquarters. Mastery of the digital battlefield requires both global reach and local tactical precision.
Mastering the Intersection: Why Strategic Advisory Outlasts Software Alone
The digital battlefield of 2026 moves too fast for "set-and-forget" software. While many cybersecurity companies provide powerful tools, those tools are only as effective as the strategy guiding them. Relying solely on automated platforms creates a dangerous sense of complacency. If you treat security as a mere IT cost rather than a core leadership discipline, you're leaving your organization vulnerable to the $5.2 million average cost of a data breach. Mastery in this era requires more than a license; it demands a definitive bridge between technical complexity and business governance.
Successful organizations understand that software is a tactic, while resilience is a strategy. This is why the Cybersecurity in the Age of Artificial Intelligence framework has become the ultimate guide for modern executives. It moves you past the "tool sprawl" that plagues the $311 billion vendor market and focuses on actionable frameworks that align with your organizational goals. Dr. Daniel Glauber specializes in this exact intersection, helping leaders navigate the nuances of adversarial AI while maintaining a firm grip on foundational security principles.
From Vulnerability to Mastery
Building a cyber-resilient culture starts at the top. Executive workshops are essential for transforming security from a technical hurdle into a competitive advantage. These sessions empower your leadership team to understand neural network risks without needing a PhD in data science. Keynote speaking engagements further this mission by aligning the entire organization on the gravity of the 2026 threat landscape. For long-term growth, a monthly vCISO retainer provides the steady, expert oversight necessary to manage the 13.8% CAGR growth in the security sector. This strategic partnership ensures that your defense strategy evolves as quickly as the "agentic AI" systems used by modern attackers.
Next Steps for 2026 Readiness
Your path to mastery begins with a clear-eyed assessment of your current risks. Initiating an AI risk assessment with a specialized ai cybersecurity consultant is the most effective way to identify vulnerabilities in your autonomous systems. You don't want to discover a flaw in your neural network defense after an incident occurs. Preparing for the next wave of innovation requires a pragmatic visionary approach that balances the dual nature of AI as both a threat and a defense. Secure your organization's future today by moving beyond software and embracing a framework of strategic mastery. The window for proactive defense is closing; the time for decisive leadership is now.
Forging a Path to Strategic Resilience
The digital battlefield of 2026 demands a fundamental shift from passive tool acquisition to active executive leadership. You've seen that the most effective cybersecurity companies aren't merely software vendors; they're partners in governance who bridge the gap between complex neural networks and board-level business risk. By prioritizing AI resilience and applying a structured vetting framework, you move your organization from a state of potential vulnerability to one of strategic mastery. Success in this era isn't defined by the number of tools in your stack, but by the strength of the leadership guiding them.
Dr. Daniel Glauber brings over 30 years of technology and innovation experience to help you navigate this rapidly evolving landscape. As the author of "Cybersecurity in the Age of Artificial Intelligence" and a trusted vCISO for global organizations, he provides the definitive, actionable frameworks needed to secure your critical domains. It's time to move beyond the marketing hype and embrace a pragmatic, visionary approach to defense. Secure your organization's future with Dr. Glauber's Strategic Advisory Services. You have the knowledge and the framework to lead; now is the time to act with confidence and precision.
Frequently Asked Questions
What are the top cybersecurity companies to watch in 2026?
Leading cybersecurity companies in 2026 are those that have successfully integrated agentic AI into their core detection engines. You should monitor firms that prioritize zero-trust architecture and demonstrate compliance with the September 11, 2026, EU Cyber Resilience Act. While market size is projected to reach $311 billion this year, the top performers are those that move beyond signature-based detection to offer autonomous, self-healing network capabilities.
How do I choose between a global security firm and a local vCISO?
You should choose a global firm for high-fidelity toolsets and a local vCISO for strategic, region-specific governance. Global vendors provide the "firepower" of advanced EDR and NDR platforms. A local strategic advisor, however, understands the nuances of regional regulations and provides the leadership necessary to translate technical telemetry into board-level business value. This dual approach ensures both tactical strength and strategic alignment.
Is AI in cybersecurity just marketing hype, or is it a real defense?
AI is a critical defense mechanism when it moves beyond basic automation to include autonomous self-healing and predictive analytics. Real AI defense is defined by its ability to counter adversarial AI attacks that manipulate neural networks. Without these capabilities, your organization remains vulnerable to machine-speed threats that bypass traditional firewalls. Effectiveness is measured by the reduction in response latency, not just the presence of a chatbot.
What questions should the Board ask potential cybersecurity partners?
The Board must ask how a partner quantifies ROI and how they ensure compliance with the SEC's four-day incident disclosure rule. They should also inquire about the partner's strategy for managing "Shadow AI" and their ability to provide actionable risk reporting. It's vital to know if the partner can prove their own AI models haven't been compromised by poisoned training data or adversarial logic.
Can a single cybersecurity company protect against all AI-driven threats?
No single vendor can provide absolute protection against every autonomous threat vector. You need a layered defense strategy that integrates best-in-breed tools with high-level strategic oversight. While tool sprawl creates operational risk, a unified framework allows different systems to share data harmoniously. Success depends on selecting partners that prioritize API-first architectures and seamless interoperability over closed, proprietary ecosystems.
How much should an organization invest in cybersecurity companies annually?
Organizations typically invest between $175 and $400 per user per month for advanced managed security packages in 2026. For strategic leadership, vCISO services often range from $2,500 to $15,000 per month on a retainer basis. These investments are necessary to mitigate the average breach cost, which has now climbed to over $5.2 million for mid-market enterprises. Budget allocation should prioritize strategic advisory alongside technical tools.
What is the difference between a managed security provider and a strategic advisor?
A managed security provider focuses on tactical monitoring and alert response, while a strategic advisor focuses on leadership and governance. Managed providers act as your 24/7 "eyes on glass" in the SOC. Strategic advisors, conversely, bridge the gap between IT and the C-suite, ensuring that your security posture aligns with long-term business objectives and the February 2026 CISA directives on edge devices.
How does Dr. Daniel Glauber's framework differ from standard vendor offerings?
Dr. Daniel Glauber's framework focuses on the "Intersection of AI and Cybersecurity" to provide actionable strategies rather than just technical software. While standard cybersecurity companies sell tools, this approach provides a comprehensive curriculum of 18 chapters and 50+ real-world case studies. It prioritizes the "Expert Practitioner" model, moving your organization from a state of vulnerability to one of mastery through disciplined research and pragmatic leadership.




