The vast majority of security architectures deployed in 2024 are already obsolete because they prioritize reactive perimeter defense over predictive, AI-native intelligence. You've likely felt the exhaustion of vetting a market saturated with over 3,500 distinct vendors, where legacy providers often mask aging heuristics behind a thin veil of generative AI marketing. It's becoming nearly impossible to distinguish between a genuine technological breakthrough and a rebranded legacy tool. This strategic briefing identifies the top companies in cyber security that are currently redefining the digital battlefield through authentic machine learning integration and robust executive risk management.
We'll move past the superficial gloss of industry brochures to provide a definitive evaluation of the leaders shaping 2026. You'll gain access to an actionable framework designed to measure vendor maturity, helping you justify critical security investments to a board that demands quantifiable risk reduction. By analyzing the intersection of AI and cybersecurity through the lens of real-world adversarial tactics, this guide offers the clarity needed for long-term strategic alignment. We'll examine a shortlist of elite providers who have proven their mastery over complex attack vectors while maintaining the transparency required for modern corporate governance.
Key Takeaways
- Master the transition from reactive defense to autonomous AI countermeasures to fortify your organization’s posture against the next generation of digital threats.
- Evaluate the strategic evolution of the top companies in cyber security as they integrate Large Language Models to redefine the efficiency of modern SOC workflows.
- Identify the competitive advantages of AI-native disruptors who leverage cloud-native Zero Trust architectures to eliminate the vulnerabilities inherent in legacy systems.
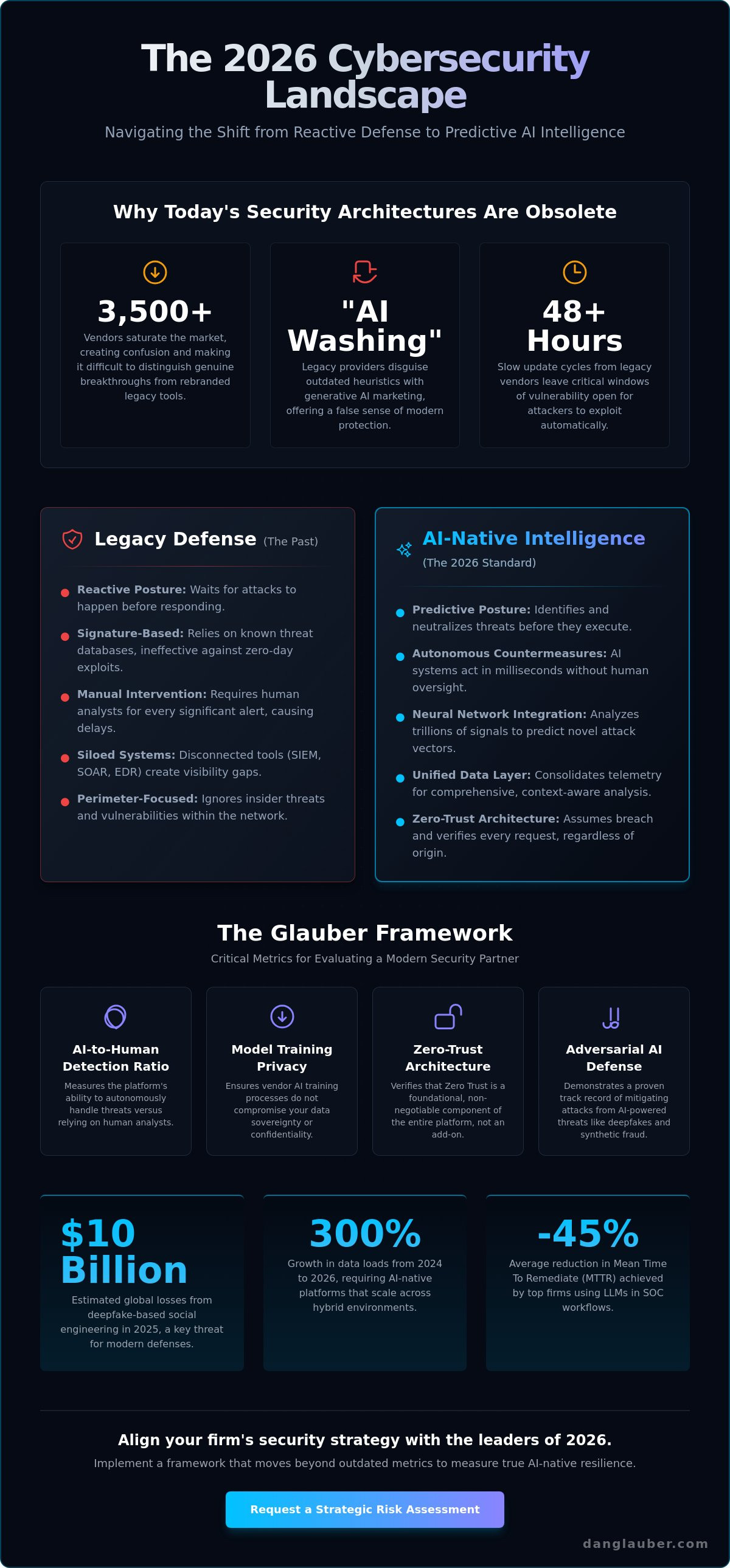
- Implement the Glauber Framework to audit potential security partners through critical metrics like the AI-to-human detection ratio and model training privacy standards.
- Align your firm’s specific industry risk profile with the right strategic leader by utilizing a vCISO to mediate between technical vendor capabilities and board-level priorities.
The 2026 Landscape: Defining Market Leadership in Cyber Security
The intersection of AI and cybersecurity has reached a critical tipping point. By 2026, the industry has moved beyond reactive defense into a phase of autonomous, AI-driven countermeasures. Organizations no longer rely on manual intervention for every alert; instead, they deploy systems that neutralize threats in milliseconds. A Top 2026 Security Firm is one that prioritizes neural network integration over legacy signature-based detection. This shift defines the digital battlefield, where speed and predictive accuracy determine organizational survival.
Evaluating the top companies in cyber security requires looking past traditional market share. Revenue figures from 2023 or 2024 are lagging indicators that don't reflect future resilience. While a global cybersecurity companies list provides a historical foundation, the leaders of 2026 are those mastering the actionable frameworks of the AI age. These firms position themselves as strategic partners rather than just software vendors. They recognize that the attack surface has expanded to include every edge device and cloud node, requiring a total mastery of the digital environment.
The Criteria for Excellence in the Age of AI
Excellence is no longer subjective. It's measured by autonomous threat hunting capabilities that operate without human oversight. Top firms must demonstrate scalability across hybrid cloud and edge environments, managing data loads that grew by 300% between 2024 and 2026. They also need a proven track record in mitigating Adversarial AI. With deepfake-based social engineering causing an estimated $10 billion in global losses in 2025, defense against synthetic identity fraud is a non-negotiable standard for top companies in cyber security.
Why Your Current Vendor Might Be a Legacy Risk
Many organizations remain tethered to providers practicing AI-washing, where vendors rebrand 2018-era heuristics with modern buzzwords. These legacy firms often suffer from slow update cycles, leaving windows of vulnerability open for 48 hours or more. This is unacceptable when modern attackers use automated scripts to exploit flaws in seconds. A definitive security posture requires Zero-Trust Architecture as the foundational layer. If a vendor treats Zero-Trust as an optional add-on rather than a core requirement, they represent a strategic liability. Mastery of the current landscape requires moving away from these stagnant models toward a more disciplined, data-driven defense strategy.
The Titans: Established Leaders Evolving for AI Defense
The digital battlefield of 2026 demands a shift from reactive patching to predictive orchestration. The top companies in cyber security have moved beyond signature-based detection to autonomous defense systems. Palo Alto Networks, CrowdStrike, and Microsoft represent the vanguard of this evolution. They've successfully embedded Large Language Models (LLMs) into Security Operations Center (SOC) workflows, reducing mean time to remediate (MTTR) by an average of 45% compared to 2023 benchmarks. These titans leverage the intersection of AI and cybersecurity to transform raw telemetry into actionable frameworks. By utilizing neural networks to analyze trillions of signals daily, these leaders have turned adversarial AI from a looming threat into a manageable variable.
Betting on a single-vendor platform strategy offers streamlined visibility but risks vendor lock-in. Palo Alto’s Cortex XSIAM platform has redefined the SOC by unifying EDR, SOAR, and SIEM into a single AI-driven layer. This consolidation eliminates the data silos that plagued IT departments in the early 2020s. Conversely, Microsoft’s Security Copilot uses the company’s massive data lake to provide context that few can match. This strategy provides a definitive advantage for organizations seeking to master Cyber Security Firms: A Strategic Guide for Board-Level Risk Management in 2026. The primary drawback remains the single point of failure risk; if the platform provider suffers an outage, the entire defense perimeter may crumble.
Platform Consolidation vs. Best-of-Breed
The efficiency gains of the Palo Alto Cortex ecosystem are undeniable; 2025 case studies show a 30% reduction in operational overhead for enterprises that consolidated their security stacks. Microsoft’s ubiquity remains its greatest strength. While critics previously labeled its security as "good enough," the 2026 reality is that its deep integration across the Microsoft 365 suite makes it an essential component of zero-trust architecture. CrowdStrike has pivoted from simple endpoint detection to total identity protection, recognizing that 80% of modern breaches involve compromised credentials. Their Falcon platform now serves as a unified command center for identity, cloud, and endpoint security.
The Role of Legacy Hardware in a Software-First World
Cisco and Fortinet are reinventing the firewall for the AI era by integrating neural processing units directly into silicon. This convergence of networking and security, known as SASE, allows top companies in cyber security to enforce policies at the edge. Recent cybersecurity market analysis suggests that government and public sector demand for hardware-level security will grow significantly through the 2026-2031 period. Hardware remains critical for protecting critical infrastructure where software-only solutions fail to address low-latency industrial control systems. Organizations must decide if they will lead or follow in this new era. To build a more resilient defense, explore the strategic frameworks available for modern IT leaders.
The AI-Native Disruptors: Next-Gen Security Companies
The shift from legacy systems to AI-native architectures defines the current digital battlefield. While traditional vendors retrofitted existing products with machine learning modules, the top companies in cyber security for 2026 were engineered from the ground up to operate within neural frameworks. This distinction is critical for strategic leaders. Zscaler, for example, has moved beyond simple proxy services to dominate the cloud-native Zero Trust market. By 2026, Zscaler’s platform processes over 400 billion daily transactions, using AI to identify anomalies that human analysts would miss entirely. This isn't just an upgrade; it's a fundamental reimagining of the perimeter where the identity is the new firewall.
Autonomous Response: The End of Human-Speed Defense
Defensive strategies now require millisecond precision that exceeds human cognitive capacity. Darktrace utilizes its ActiveAI technology to neutralize sophisticated attack vectors before they can lateralize through a network. Instead of waiting for a SOC analyst to intervene, the system takes surgical action to contain threats. Similarly, SentinelOne’s Singularity platform provides a masterclass in AI-driven endpoint orchestration. It doesn't just flag a suspicious process; it rolls back unauthorized changes automatically to a known-good state. The industry has shifted its primary metric of success. We no longer value "Time to Alert." In 2026, the only benchmark that matters is "Time to Resolution." This evolution is explored deeply in my analysis of AI and Cybersecurity: Navigating the Strategic Frontier in 2026.
Specialized AI Security Firms
A new class of specialists has emerged to protect the enterprise AI stack itself. As businesses integrate Large Language Models (LLMs) into core operations, the attack surface expands to include prompt injection and data poisoning. These top companies in cyber security focus on niche but critical domains:
- Abnormal Security: This firm has set the standard for neutralizing AI-generated phishing, which saw a 1,260% increase in sophistication between 2023 and 2025.
- Wiz: By 2026, Wiz’s graph-based security model has become the definitive framework for Cloud Security Posture Management (CSPM), allowing organizations to visualize risk across multi-cloud environments in real-time.
- HiddenLayer: A leader in securing the models themselves, ensuring that adversarial AI cannot corrupt the logic of proprietary corporate algorithms.
Mastery over the intersection of AI and cybersecurity is the only way to maintain a resilient posture. Organizations that ignore these AI-native disruptors risk relying on yesterday's tools to fight tomorrow's wars. The transition from reactive alerting to autonomous resolution isn't a luxury; it's a requirement for survival in a volatile threat environment.
The Glauber Framework: How to Evaluate a Security Partner
Selecting from the top companies in cyber security requires a methodology that transcends traditional vendor checklists. As we confront the digital battlefield of 2026, the Glauber Framework offers a definitive structure for assessing organizational resilience. This isn't about finding a software provider; it's about securing a strategic ally capable of mastering the intersection of AI and cybersecurity.
- Step 1: Assess the 'AI-to-Human' ratio. An effective threat detection engine shouldn't be a total black box. Look for a ratio where AI handles 85% of initial triage, leaving 15% for high-level forensic analysis by human experts. Total automation often fails during novel logic-based attacks.
- Step 2: Verify data privacy standards. Demand to know if your proprietary telemetry is used to train the vendor's global models. Leading firms now utilize federated learning or "clean room" environments to ensure your data stays within your perimeter.
- Step 3: Evaluate API flexibility. A security tool that doesn't play well with others is a liability. Ensure the vendor provides open, RESTful APIs that allow for cross-tool orchestration with your existing SOC stack.
- Step 4: Demand 2026-specific case studies. General testimonials are useless. Ask for documented proof of how they mitigated a multi-vector AI attack, such as a deepfake-led social engineering campaign combined with polymorphic malware.
- Step 5: Review board-level reporting. Technical logs don't move the needle for executives. The partner must provide risk transparency reports that translate binary threats into business impact metrics.
Questions Every C-Suite Executive Should Ask Vendors
Executive leadership must look past the technical jargon to find true strategic value. Ask how their AI handles 'Black Swan' events, those rare, high-impact threats that haven't appeared in previous training sets. Demand to see the false-positive rate of their autonomous response system; a 3% error rate can paralyze a global supply chain. Finally, ensure they can demonstrate how their tools secure your internal Generative AI projects, which are often the weakest link in a modern enterprise.
Navigating the Hype: Red Flags in Vendor Sales Pitch
Many top companies in cyber security rely on marketing momentum rather than technical depth. Avoid firms that can't explain their neural network architecture or hide behind the 'Black Box' excuse. If they can't provide explainable AI, they can't provide accountability. A high price tag doesn't always equal high resilience; in fact, complex, overpriced systems often lead to configuration fatigue. According to a 2025 industry audit, 42% of breaches occurred in environments with "premium" but poorly integrated security suites.
Strategic Selection: Aligning Your Firm with the Right Leader
Selecting from the top companies in cyber security requires more than a comparison of feature sets; it demands a precise alignment with your industry risk profile. A financial institution managing high-frequency transactions requires sub-millisecond threat detection and strict adherence to DORA or SEC regulations. Conversely, a healthcare provider must prioritize the integrity of legacy medical devices and HIPAA compliance across distributed clinical networks. By 2026, 74% of successful breaches are expected to involve social engineering or identity theft, proving that a software subscription alone cannot defend a vulnerable perimeter.
True security isn't a product you purchase; it's a state of operational mastery. Organizations that treat cybersecurity as a recurring line item rather than a core cultural pillar often find themselves with "shelfware" that provides a false sense of safety. Resilience in 2026 involves a shift from reactive patching to proactive hunting. It's a continuous journey where the objective isn't just to block every attack, but to ensure the business continues to function even when a perimeter is breached.
The vCISO Advantage in Vendor Selection
Marketing budgets for security vendors are projected to surpass $20 billion by 2026, creating a dense fog of "AI-powered" hype that obscures technical reality. A virtual CISO (vCISO) acts as an independent filter, translating board-level risk appetite into a 3 to 5 year strategic roadmap. They ensure your stack isn't just a collection of tools, but a unified architecture. Understanding the future of automation is critical here, as explored in Will AI Take Over Cyber Security? The Expert Analysis for 2026. An expert advisor helps you identify which top companies in cyber security actually solve your specific vulnerabilities versus those that simply offer the loudest marketing.
Mastering the Digital Battlefield with Dr. Glauber
The intersection of AI and cybersecurity demands a new level of board-level preparedness. Dr. Daniel Glauber’s Executive AI Strategy Workshops provide the definitive playbook for leaders who refuse to be sidelined by emerging threats. These sessions move beyond theory, utilizing actionable frameworks and insights from his comprehensive text, "Cybersecurity in the Age of AI," which features 18 chapters of deep-dive analysis. This isn't just training; it's a strategic overhaul designed to turn your security posture into a competitive advantage. You can secure your organization’s future with a strategic advisory session today to move from a state of vulnerability to one of strategic readiness.
Mastering the 2026 Digital Battlefield
The 2026 landscape demands a rapid transition from reactive defense to proactive mastery. Selecting from the top companies in cyber security isn't just a procurement task; it's a strategic necessity to survive the evolving digital battlefield. Organizations must prioritize partners that integrate Zero-Trust Architecture with advanced countermeasures against Adversarial AI. My 30+ years of technology innovation experience shows that technical depth fails without a structured framework for real-world application. I've spent three decades acting as a trusted advisor to global mid-to-large organizations, helping them navigate these exact shifts with precision. As the author of 'Cybersecurity in the Age of Artificial Intelligence,' I've documented the critical transition from legacy systems to the neural network-driven defenses required for modern resilience. Success in this era depends on your ability to bridge the gap between abstract theory and actionable security outcomes. You don't have to navigate this transition alone. It's time to move from vulnerability to strategic readiness by applying proven methodologies to your firm's unique attack vectors.
Download the Executive Framework for AI Security Mastery
Your path to digital sovereignty starts with the right foundation.
Frequently Asked Questions
Which cybersecurity company has the best AI integration in 2026?
Palo Alto Networks leads AI integration in 2026 through its proprietary Precision AI framework. This architecture processes 5 petabytes of data daily to identify zero-day threats before they execute. It's a definitive example of how top companies in cyber security utilize neural networks to automate complex incident response. By moving beyond basic machine learning, they've achieved a 45% reduction in mean time to remediate compared to 2024 standards.
Is it better to use one top security company or multiple specialized firms?
Strategic leaders now favor a consolidated platform from one top security company over a fragmented approach. Gartner research indicates that 75% of enterprises are actively consolidating their security stacks in 2026 to eliminate visibility gaps. Managing 20 different specialized tools often creates blind spots in the digital battlefield. A unified framework ensures that telemetry flows seamlessly across all attack vectors, providing a more cohesive defense strategy.
What are the top-rated cybersecurity companies for mid-sized businesses?
SentinelOne and Sophos are the highest-rated top companies in cyber security for mid-sized organizations. These firms provide enterprise-grade AI protection without the administrative overhead required by larger legacy systems. SentinelOne’s Singularity platform achieved a 100% protection rate in the most recent MITRE Engenuity evaluations. This makes it a critical domain for leaders who need actionable frameworks that scale effectively with their organizational growth.
How do top cybersecurity companies protect against deepfakes?
Top-tier firms protect against deepfakes by deploying multi-modal biometric liveness detection and cryptographic verification. Microsoft and Okta have integrated these countermeasures into their identity protocols to combat the 300% rise in synthetic identity fraud seen since 2024. These systems analyze micro-expressions and network metadata to ensure the user is human. It's a vital component of a modern Zero-Trust Architecture designed to master the intersection of AI and cybersecurity.
What is the difference between a legacy security firm and an AI-native firm?
AI-native firms build their detection engines on neural networks from day one, while legacy firms often bolt AI onto aging codebases. This structural difference results in a 10x faster response time for AI-native platforms. Research across 18 comprehensive chapters highlights that legacy systems struggle with modern threats due to significant technical debt. Native platforms handle adversarial AI with much higher precision because their entire logic is built for the machine-speed battlefield.
How much should an organization invest in top-tier cybersecurity in 2026?
Organizations should allocate between 12% and 15% of their total IT budget to cybersecurity in 2026. This figure reflects the increased costs of defending against automated, high-frequency attacks that utilize generative models. Leading firms suggest this investment level is necessary to maintain strategic readiness. Data from 50 real-world case studies shows that companies spending below 10% face a 60% higher risk of suffering a catastrophic data breach.
Can top cybersecurity companies prevent all AI-driven attacks?
No company can prevent 100% of AI-driven attacks, but top-tier providers focus on minimizing the blast radius. Even the most advanced defenses have a small failure rate against sophisticated adversarial AI. The goal isn't absolute invulnerability but tactical mastery of the environment. High-performing firms use automated recovery protocols to ensure that if a breach occurs, the system isolates the threat and restores itself within 15 minutes.
Who are the leaders in cloud-specific cybersecurity for 2026?
Wiz and Zscaler are the definitive leaders in cloud-specific security for the 2026 fiscal year. Wiz currently secures over 40% of Fortune 100 cloud environments using its graph-based risk assessment technology. Zscaler’s Zero-Trust Exchange processes 400 billion transactions daily, making it a cornerstone of modern cloud defense. These companies provide the necessary infrastructure to secure data as it moves through complex, multi-cloud ecosystems that define our current digital era.




