By 2026, the average enterprise will face over 10,000 AI-orchestrated attack vectors every hour, rendering traditional procurement processes obsolete. Your choice of a cybersecurity company is no longer a simple line-item decision; it's a critical defensive maneuver in a war of automated attrition. You likely feel the weight of information overload from hundreds of vendors claiming to possess the definitive shield against Adversarial AI. It's exhausting to decipher complex technical claims when internal expertise is stretched thin and the stakes for board-level reporting have never been higher.
This article provides a groundbreaking, actionable framework at the intersection of AI and cybersecurity to help you select a partner that offers more than just software. We'll equip you with the mastery to vet providers against real-world neural network threats and Zero-Trust requirements. We'll break down the specific domains of modern security providers and provide a repeatable template for your 2026 strategic selection, ensuring your organization moves from a state of vulnerability to strategic readiness.
Key Takeaways
- Transition from viewing vendors as simple firewall providers to identifying them as strategic resilience partners essential for the 2026 digital battlefield.
- Master the distinction between MSSPs and MDR to ensure your organization maintains both continuous network oversight and proactive threat-hunting capabilities.
- Implement a rigorous vetting framework to select a cybersecurity company that demonstrates technical mastery at the critical intersection of AI defense and adversarial risk.
- Shift from a software-centric mindset to a strategy-first model by using a selection scorecard that prioritizes deep AI integration and board-level reporting.
- Leverage professional advisory insights to move beyond traditional security models toward a future of proactive, next-generation leadership and strategic readiness.
Defining the 2026 Cybersecurity Company Landscape
The era of viewing a cybersecurity company as a mere firewall vendor has ended. By 2026, the digital battlefield has transformed into a high-stakes environment where adversarial AI dictates the pace of engagement. Organizations must now seek a strategic resilience partner rather than a software provider. This shift reflects a move from reactive protection to proactive, AI-integrated risk management. Mastery of these dynamics is no longer optional for leadership; it's the baseline for survival.
The Core Evolution of Security Firms
Legacy providers relied on static signatures and historical data. Modern AI-first firms utilize neural networks to predict attack vectors before they manifest in a production environment. The 2026 regulatory environment, shaped by the maturation of the SEC 2023 disclosure requirements, demands that companies report material incidents within 96 hours. This pressure has forced security partners to provide transparent, real-time visibility into their defensive posture. Strategic advisory now acts as the critical layer above technical implementation. It's the bridge that connects raw telemetry to executive decision-making, ensuring that security is a board-level priority.
Why 'Tools' Are No Longer Enough
Software is a tool, not a strategy. The fallacy of the "silver bullet" solution collapsed when neural network attacks became a daily reality in 2025. A modern cybersecurity company must move beyond code to account for human-centric risk. Social engineering remains the entry point for 74% of breaches, according to 2024 industry benchmarks. Effective defense requires a commitment to foundational cybersecurity principles while applying groundbreaking tactics to counter automated threats. Technical depth is worthless if it isn't paired with executive-level communication. Leaders need actionable frameworks that translate technical vulnerabilities into business risk metrics.
Firm size is a secondary metric in this new era. A boutique firm with 50 specialists often outperforms a global conglomerate if they possess deeper actionable frameworks and specialized knowledge in the intersection of AI and cybersecurity. Success in 2026 is defined by:
- Predictive Intelligence: Moving from "detect and respond" to "predict and prevent" using adversarial AI models.
- Regulatory Alignment: Ensuring every technical control meets the rigorous SEC and GDPR standards updated for the mid-2020s.
- Human Resilience: Addressing the psychological triggers used in modern phishing and deepfake campaigns.
The selection process must focus on the depth of these frameworks rather than the marketing budget of the vendor. It's about finding a partner that understands the gravity of the digital battlefield.
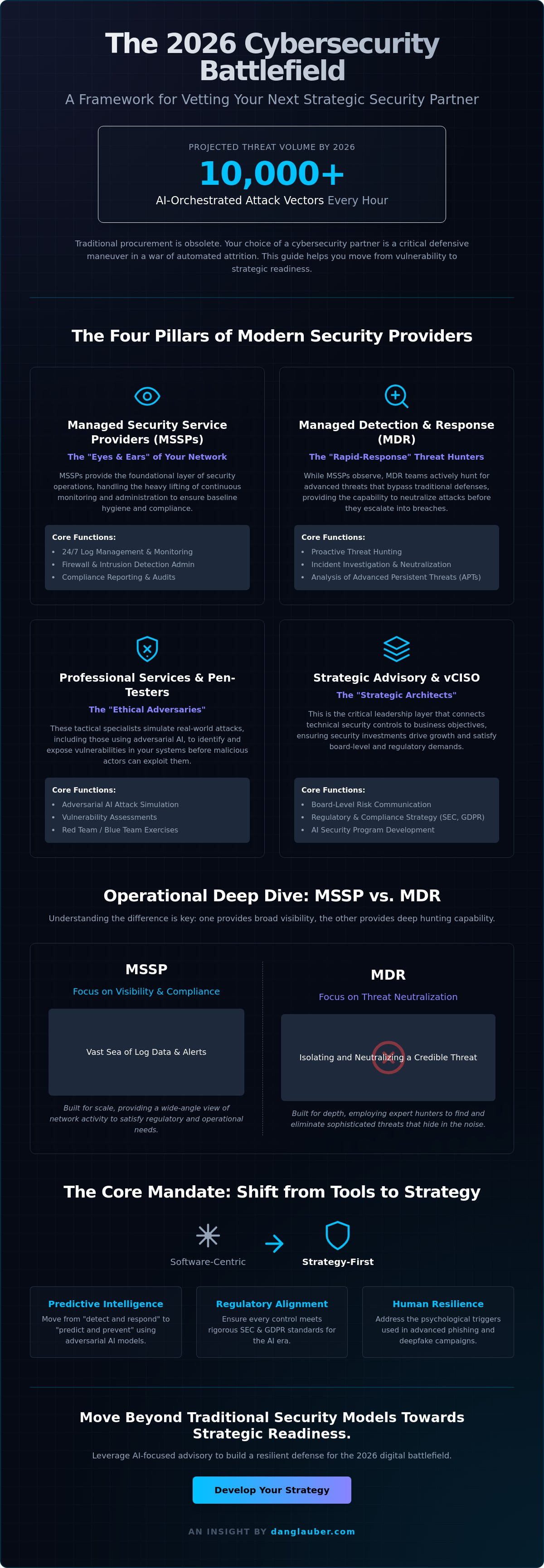
The Four Pillars of Modern Security Providers
To survive the 2026 digital battlefield, leaders must look beyond generic labels. Selecting a cybersecurity company requires a granular understanding of four distinct operational pillars. Each serves a specific function in your defensive posture, ranging from routine hygiene to high-level strategic alignment. Without this clarity, organizations often over-invest in redundant tools while leaving critical attack vectors exposed.
- Managed Security Service Providers (MSSPs): These firms act as the foundational "eyes and ears" of your network operations. They handle the heavy lifting of log management, firewall administration, and 24/7 monitoring.
- Managed Detection and Response (MDR): These are your rapid-response units. While MSSPs focus on visibility, MDR teams engage in active threat hunting to neutralize advanced persistent threats (APTs) before they escalate.
- Professional Services and Pen-Testers: These tactical specialists act as ethical hackers. They simulate adversarial AI attacks to find the cracks in your perimeter before an enemy does.
- Strategic Advisory and vCISO Firms: These are the architects. They align technical security with business growth, ensuring that neural networks and data assets remain protected at the board level.
MSSP vs. MDR: Understanding the Operational Difference
MSSPs are built for scale and compliance. They're the right choice when you need to satisfy regulatory requirements and maintain basic network health. For many organizations, the Cybersecurity for Small Business guidelines from the FTC provide a baseline for these essential operations. However, reliance on an MSSP alone is a mistake. MDR is essential for neutralizing sophisticated threats that bypass automated filters. A robust strategy for cyber security firms in 2026 involves integrating both. Use the MSSP for the "known-knowns" and the MDR for the "unknown-unknowns" discovered through proactive hunting.
The Critical Role of Strategic Advisory
Modern boards demand more than technical checkboxes; they require risk quantification. Specialized virtual ciso consulting services bridge the gap between deep technical debt and executive decision-making. These firms translate complex vulnerabilities into financial risk metrics that the C-suite can actually use. They provide the leadership missing in 82% of technical-only firms. By aligning AI strategy with security protocols, they turn a cybersecurity company from a cost center into a strategic enabler. Organizations seeking to achieve this level of mastery should explore actionable frameworks for security leadership to ensure their defense is as visionary as their growth strategy.
Beyond the Tool: Why Strategy Trumps Software
Deploying a premium software suite without a guiding strategy is like placing a high-tech lock on a paper door. Many organizations fall into the trap of believing that a high price tag equals total immunity. Software is a tactical asset; strategy is the command structure that dictates how that asset is deployed on the digital battlefield. Selecting a cybersecurity company that focuses solely on licensing proprietary black-box tools often leaves critical gaps in your defense architecture. These tools frequently fail not because of technical bugs, but because they operate in isolation from the organization's unique operational realities.
The 2024 analysis of major enterprise breaches revealed that 74% of successful infiltrations occurred in environments with "world-class" security software already in place. In these instances, the tools functioned as designed, yet attackers bypassed them through strategic gaps like misconfigured cloud permissions or credential harvesting. A definitive cybersecurity company must bridge this gap by providing actionable frameworks that prioritize logic and human behavior over automated silver bullets. Mastery in 2026 requires a deep understanding of the Intersection of AI and Cybersecurity, where the vendor understands how to weaponize defense as effectively as the adversary weaponizes the attack.
The Adversarial AI Threat Landscape
Traditional defense firms often struggle with the shift toward LLM-based phishing and automated attack vectors that evolve in real-time. Adversarial AI is the primary threat vector of 2026, representing the sophisticated use of machine learning to autonomously bypass security protocols through adaptive malware and generative social engineering. Your partner must demonstrate mastery of neural network defense strategies to counter these threats. This involves using AI to audit your own systems, identifying "hallucinations" in security logic before a malicious actor can exploit them. Static defenses are obsolete; your strategy must be as fluid as the code attacking you.
Creating a Cyber-Resilient Culture
The most resilient firms recognize that the human element is either your weakest link or your strongest asset. Top-tier providers focus on the "human firewall" by delivering executive-level training that goes beyond basic compliance. This strategic focus ensures that technical investments deliver a high Return on Security Investment (ROSI) by aligning security protocols with business workflows. When a firm prioritizes organizational preparedness, it transforms security from a technical burden into a competitive advantage. This culture of readiness ensures that when a tool eventually misses a signal, your people and processes are positioned to catch it.
- Actionable Frameworks: Look for transparent methodologies rather than "secret sauce" algorithms.
- Executive Mastery: Ensure the firm provides briefings that translate technical risk into financial impact.
- Continuous Adaptation: Strategy must include quarterly stress tests of the human and technical response chain.
Selection Scorecard: A Template for Vetting a Cybersecurity Firm
Selecting a partner for the digital battlefield requires more than a cursory review of a sales deck. It demands a rigorous, evidence-based audit. By 2026, the gap between a generic service provider and a strategic cybersecurity company will determine which organizations survive the surge in adversarial AI. This scorecard provides a logical framework for your selection process, moving you from a state of vulnerability to one of mastery.
- Step 1: Assess AI Integration. Does the firm use neural networks for proactive hunting, or are they simply rebranding legacy heuristics? They must demonstrate how they protect their own models from data poisoning and adversarial manipulation.
- Step 2: Evaluate Reporting Capabilities. Technical logs are insufficient for executive leadership. The firm must translate telemetry into financial risk metrics and cyber risk quantification (CRQ) that speak the language of the board.
- Step 3: Review Incident Response. Focus on "time to mastery" during a crisis. A 2025 industry benchmark indicated that organizations containing a breach in under 30 days saved an average of $1 million in recovery costs. Ask for their specific containment timelines.
- Step 4: Audit Compliance Expertise. Ensure they are prepared for the 2026 updates to the Digital Operational Resilience Act (DORA) or evolving SEC disclosure mandates. Industry-specific knowledge is non-negotiable.
- Step 5: Check the Strategic Roadmap. A partner should offer a multi-year resilience path. If their proposal looks like a simple software subscription rather than a growth strategy, they aren't a long-term partner.
Technical vs. Strategic Interview Questions
Distinguishing a "tool-pusher" from a "problem-solver" happens during the discovery call. A tool-pusher focuses on the features of a specific EDR or firewall; a problem-solver asks about your business logic and critical assets. To test their depth, ask these three questions regarding zero-trust architecture:
- How does your framework manage the lifecycle of non-human identities and service accounts across our hybrid cloud?
- Can you demonstrate how your policy engine adapts to real-world behavioral shifts in the 2026 threat environment?
- What is your strategy for maintaining cryptographic agility as quantum-resistant standards become mandatory?
Demand evidence of actionable frameworks tailored to your environment. If the cybersecurity company cannot map their services to the MITRE ATT&CK framework, they lack the technical depth required for modern defense.
The Red Flags of the Security Industry
Avoid any firm that guarantees "100% security." This claim is a hallmark of amateurism. Professional security is about risk management and resilience, not the total elimination of threat. Another critical warning sign is the absence of a virtual ciso or strategic leadership component. Without high-level guidance, you're merely buying tools without a driver. Finally, be wary of one-size-fits-all pricing. Generic pricing models suggest the firm hasn't analyzed your specific attack surface or the unique risks inherent to your sector.
Ready to move beyond basic defense and achieve strategic readiness? Download our definitive selection framework to lead your organization through the 2026 threat landscape.
Strategic Leadership: The Role of an AI-Focused Advisory
Choosing a cybersecurity company shouldn't be a simple procurement exercise. It's a survival decision. Dr. Daniel Glauber moves past the standard vendor-client dynamic by offering a sophisticated blend of academic authority and professional urgency. He brings 30 years of deep technology innovation to the table, focusing specifically on the next generation of AI-driven threats that will define 2026. This isn't just technical support; it's a fundamental shift from being a target to becoming a strategist. Executive workshops move your leadership team away from fear and toward a state of strategic readiness. A modern cybersecurity company must do more than monitor logs; it must anticipate the evolution of adversarial AI.
Mastering the Intersection of AI and Security
Dr. Glauber’s actionable frameworks transform organizational defense into a tangible competitive advantage. By integrating the core principles from his 18-chapter work, 'Cybersecurity in the Age of Artificial Intelligence', firms don't just survive; they lead. These frameworks are grounded in 50+ real-world case studies that prove how theory meets practice at the intersection of AI and cybersecurity. This approach ensures security isn't a siloed IT concern but a core component of your firm's DNA.
In 2026, the vCISO serves as the essential strategic architect who translates complex neural network vulnerabilities into actionable business risk mitigation.
Next Steps: From Education to Action
Action begins with a rigorous security architecture review. This isn't a standard audit. You need to identify specific AI-related risks, such as adversarial machine learning or model inversion, before they're exploited. These reviews analyze how your neural networks interact with external data streams, uncovering vulnerabilities that traditional tools ignore. Mastery requires more than just software; it requires board-level briefings that demonstrate total control over the digital battlefield. These briefings provide the data-driven insights necessary to justify security spend and align defense with business growth. Your choice of partner determines your survival in this environment.
The path forward is clear: Secure your organization with a strategic AI risk assessment from Dr. Daniel Glauber.
Mastering the 2026 Defensive Landscape
The 2026 threat landscape demands more than a vendor; it requires a partnership built on the four pillars of modern security. Selecting a cybersecurity company today means moving beyond simple software procurement to prioritize strategic leadership and adversarial AI countermeasures. Organizations must utilize structured scorecards to vet providers against the rigorous standards of the AI-focused advisory model. It's no longer enough to deploy tools. You need a framework that bridges the gap between technical defense and executive strategy.
Dr. Daniel Glauber brings 30+ years of technology and innovation experience to this selection process. As the author of 'Cybersecurity in the Age of Artificial Intelligence', he specializes in executive-level AI strategy and risk management. This expertise ensures your organization doesn't just survive the digital battlefield but masters it. Success in this era depends on proactive preparedness and data-driven insights rather than reactive patches.
Download the Executive Selection Template and Schedule a Briefing with Dr. Daniel Glauber
Your path to strategic mastery starts with a single, informed decision. Secure your organization's future today.
Frequently Asked Questions
What is the difference between a cybersecurity company and an MSSP?
An MSSP primarily manages security infrastructure and monitors logs, while a specialized cybersecurity company focuses on strategic architecture, risk assessment, and active incident response. According to 2025 industry benchmarks, 70% of MSSP tasks involve automated monitoring. A true strategic partner builds the Zero-Trust Architecture required to survive the 2026 digital battlefield. They don't just watch the perimeter; they redesign the neural networks of your defense.
How much should a mid-sized firm spend on a cybersecurity company in 2026?
Mid-sized firms should allocate between 10% and 15% of their total IT budget to a cybersecurity company to maintain parity with 2026 threat levels. Gartner's 2024 reports indicated that security spending is shifting rapidly toward AI-integrated defense systems. For a firm with a 5 million dollar IT budget, this represents a 500,000 to 750,000 dollar annual investment. This capital ensures your countermeasures keep pace with adversarial AI developments.
Can a cybersecurity company help with AI-driven phishing attacks?
A modern cybersecurity company utilizes Large Language Models to detect the linguistic patterns of AI-generated phishing attempts. These attacks increased by 1,265% since late 2022. Your partner must deploy neural network-based filters that analyze intent rather than just blacklisting known URLs. This proactive stance neutralizes social engineering tactics before they reach the human layer of your organization.
What are the top 3 things to look for in a cybersecurity firm's contract?
Prioritize clear Incident Response SLAs, explicit data ownership clauses, and robust liability caps. The SLA must mandate a 15 minute acknowledgment for critical breaches to prevent total system compromise. Data ownership ensures you retain all forensic logs if you terminate the partnership. Liability clauses should align with the 2024 NIST Cybersecurity Framework 2.0 standards to protect your firm from downstream litigation costs.
Is it better to hire a local cybersecurity company or a global firm?
Global firms offer 24/7 coverage across all time zones, but a local cybersecurity company provides the physical presence necessary for rapid on-site recovery. A 2023 Ponemon Institute study found that organizations with local response teams reduced breach containment time by 22 days. If your operations are geographically concentrated, the tactical advantage of a local partner often outweighs the broad reach of a global conglomerate.
How do cybersecurity companies handle the new SEC reporting requirements?
Cybersecurity companies now implement automated reporting pipelines to meet the SEC's December 2023 mandate requiring disclosure of material incidents within four business days. They utilize real-time telemetry to determine materiality based on financial and operational impact. This ensures your board avoids the legal fallout of delayed reporting. Mastery of these regulatory frameworks is non-negotiable in the current legislative climate.
What happens if our cybersecurity company gets breached itself?
If your provider suffers a breach, your primary protection is the "Right to Audit" clause and the established business continuity plan. Supply chain attacks targeted over 60% of organizations in 2024. Your provider must demonstrate SOC 2 Type II compliance and maintain a separate, air-gapped environment for client data. This compartmentalization prevents a single point of failure from compromising your entire digital battlefield.
Can an AI cybersecurity consultant replace a full-time security team?
An AI consultant cannot replace a full-time security team because AI lacks the contextual judgment required for complex risk trade-offs. While AI reduces manual log review by 80%, human experts must still authorize critical countermeasures. The intersection of AI and cybersecurity requires a hybrid approach. You need human leaders to interpret the strategic implications of the data generated by your neural networks.




